Clarity in every certified step
Turning complex IT asset workflows into traceable, verifiable processes — combining accuracy, certified standards, and real-time visibility to help teams operate with total confidence.
Trusted by organizations where security and accuracy matter most









Secure, certified, and operationally rigorous IT asset disposition.
Aligned with the security, operational, and regulatory demands of modern IT organizations.
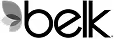
Turn ITAD into a controlled, auditable system
End-to-end IT asset disposition programs designed for enterprise IT, security, and governance teams.
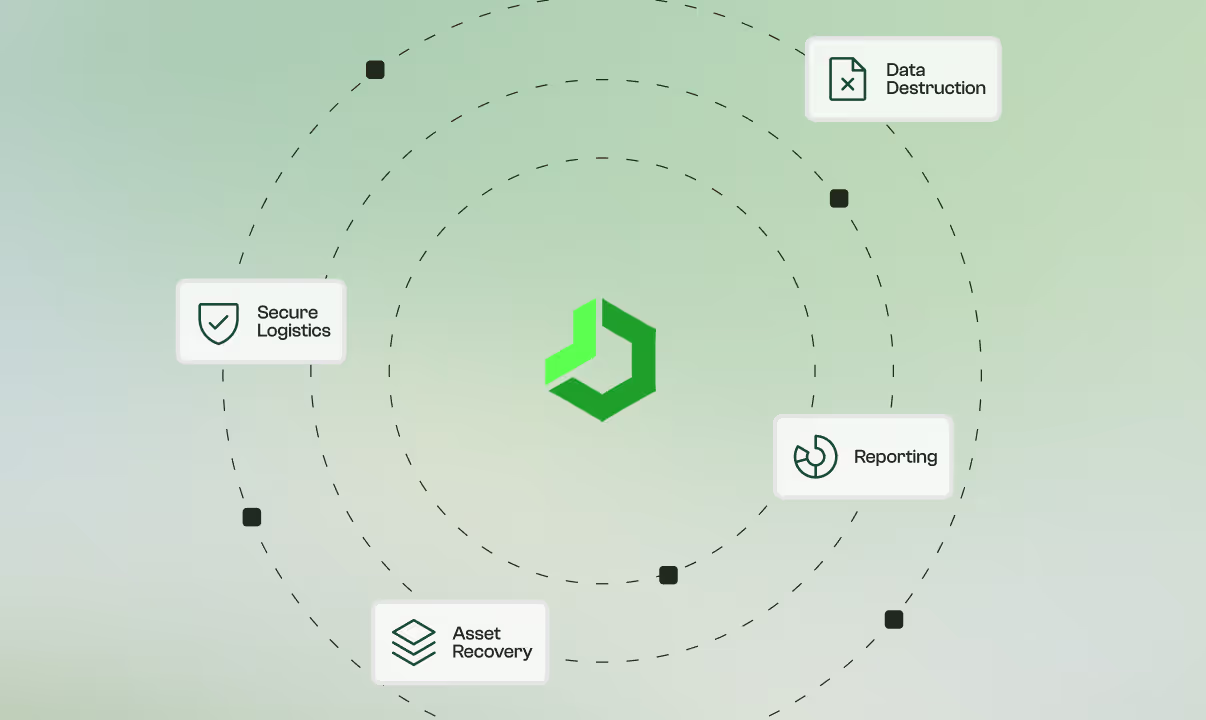
Bring data destruction under verified, certified control
Documented, controlled hardware removal for servers, storage, and networking equipment.
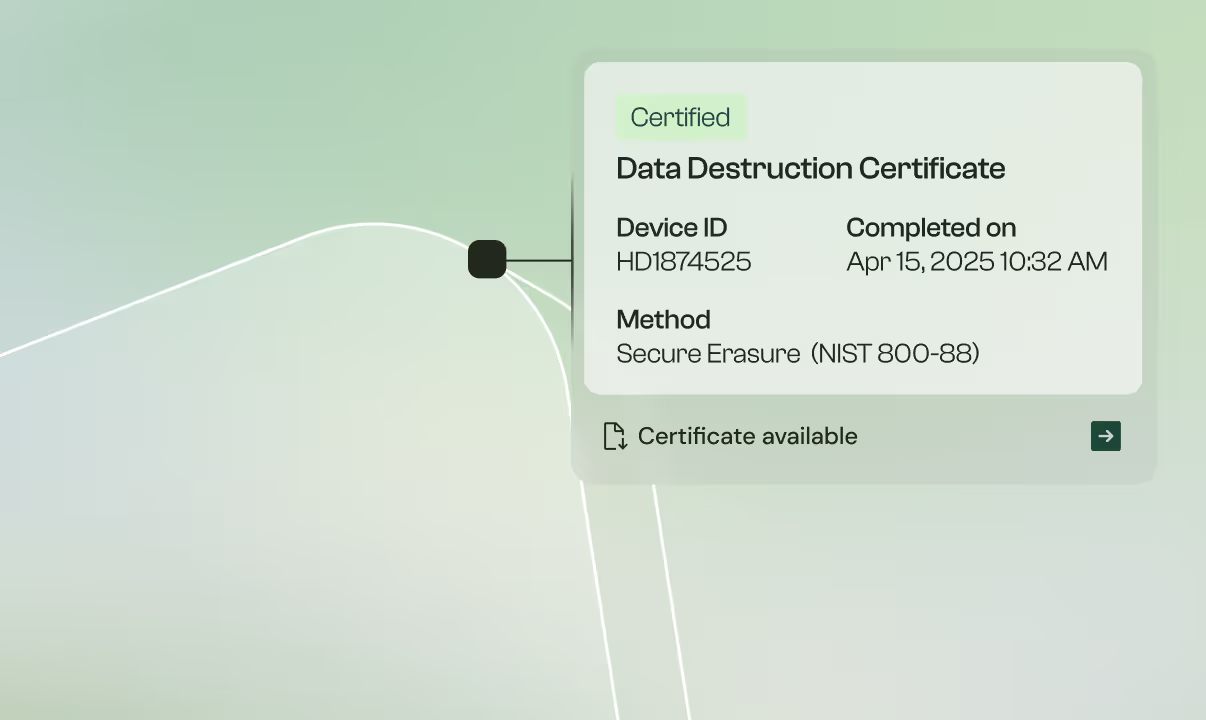
Secure hardware logistics with end-to-end traceability
End-to-end IT asset disposition programs designed for enterprise IT, security, and governance teams.
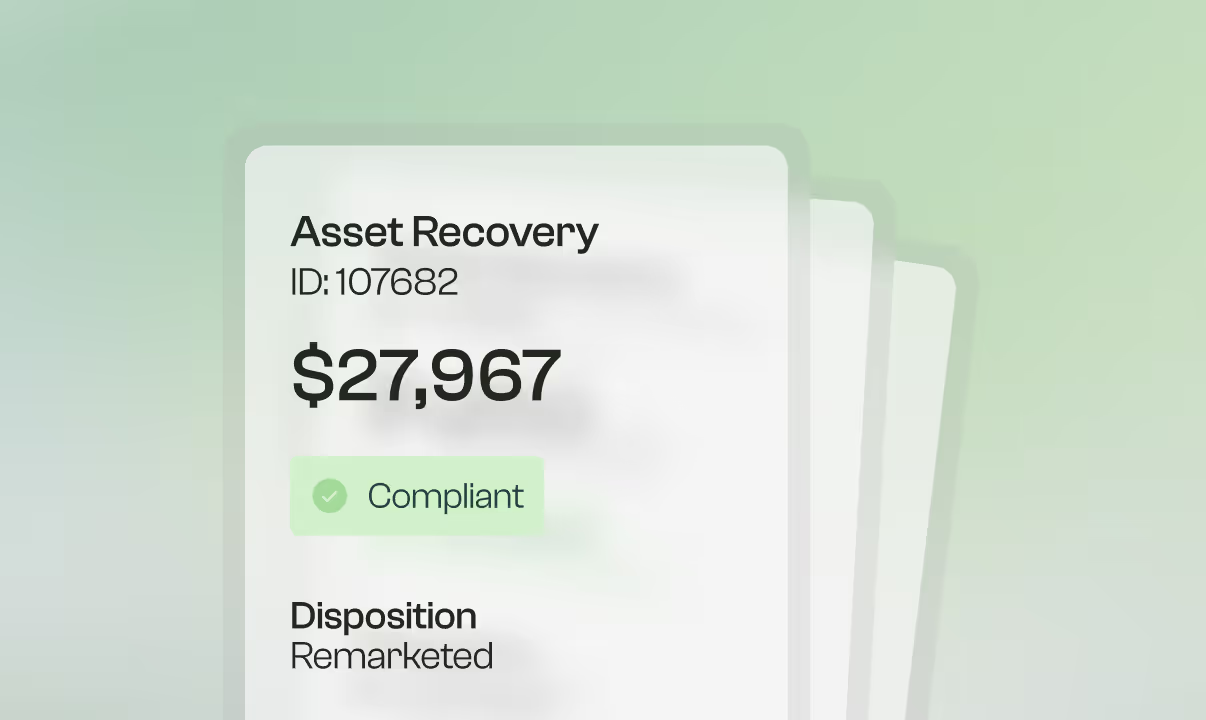
Recover asset value without compromising compliance
Documented, controlled hardware removal for servers, storage, and networking equipment.
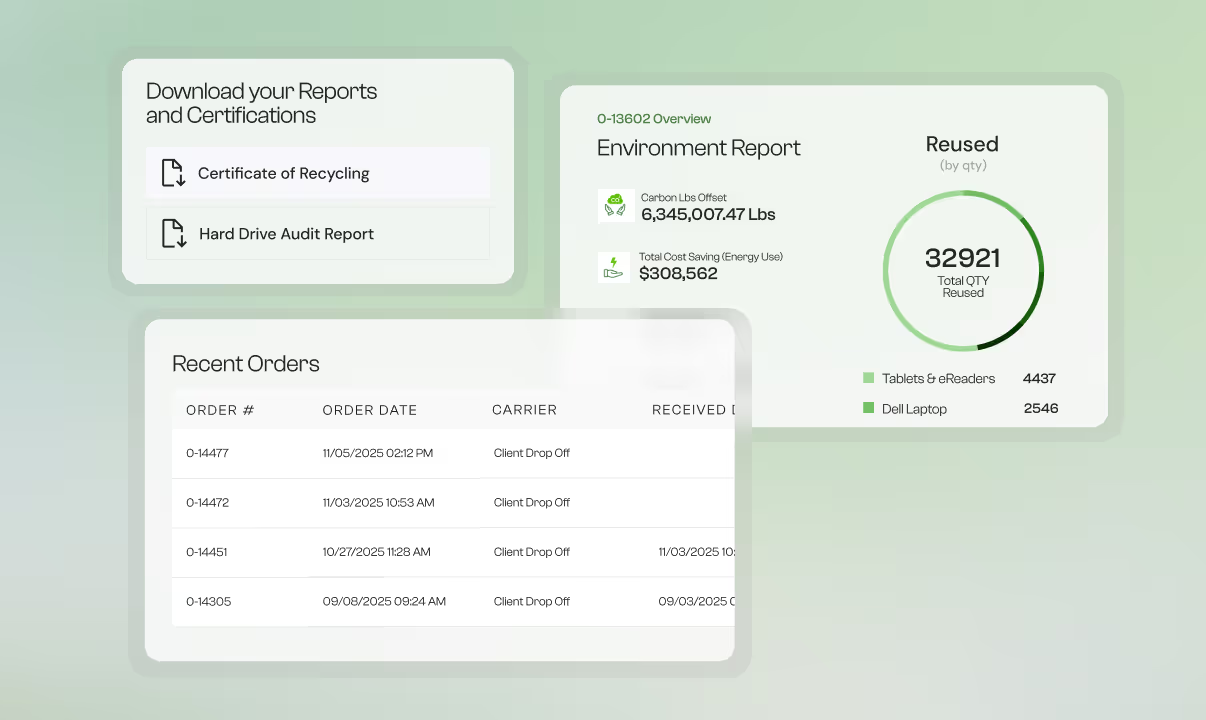
Maintain continuous audit readiness through real-time reporting
End-to-end IT asset disposition programs designed for enterprise IT, security, and governance teams.
Certifications that satisfy enterprise governance requirements




Purpose-built ITAD for regulated environments
Supporting environments where certification and documentation are essential.
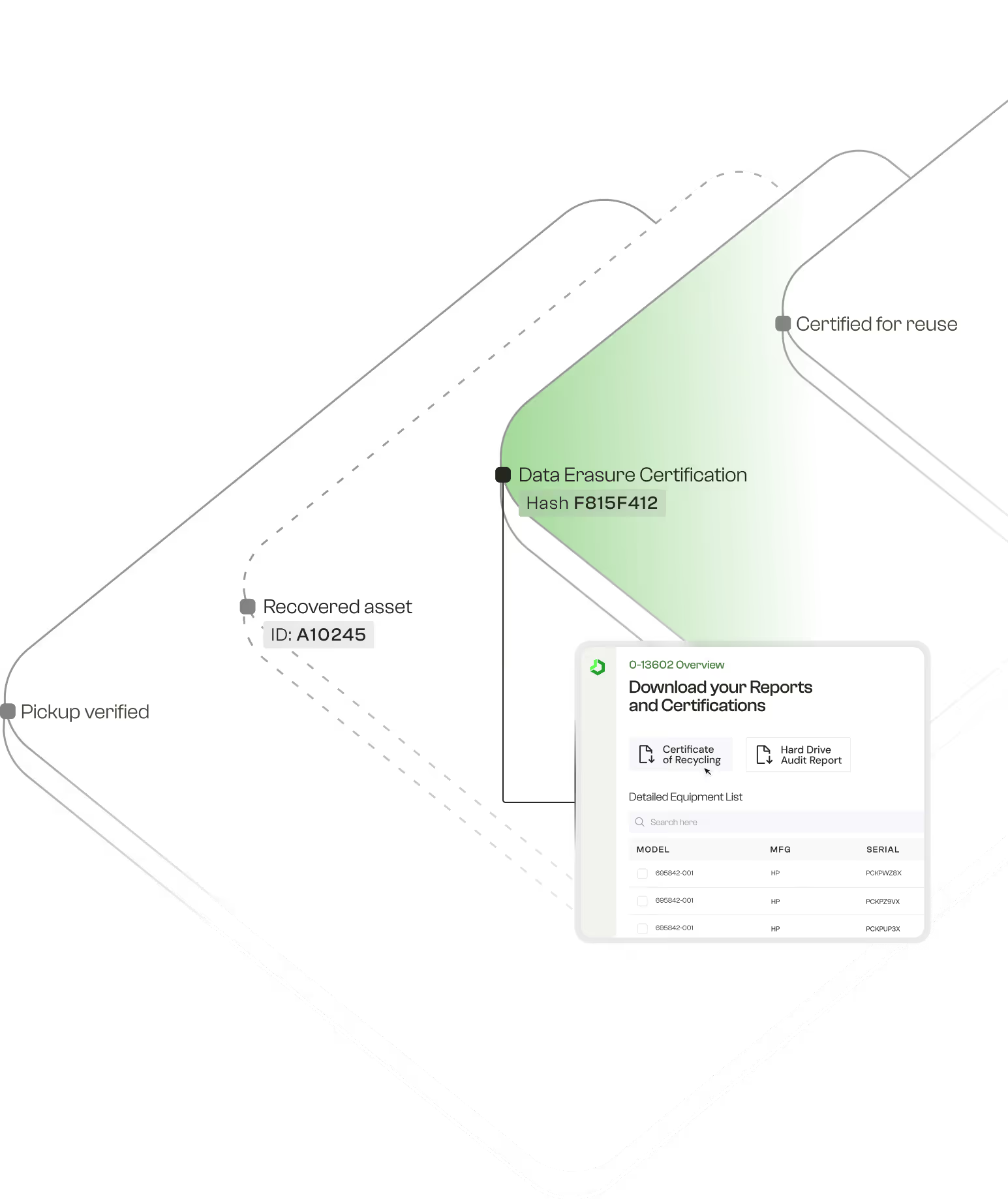
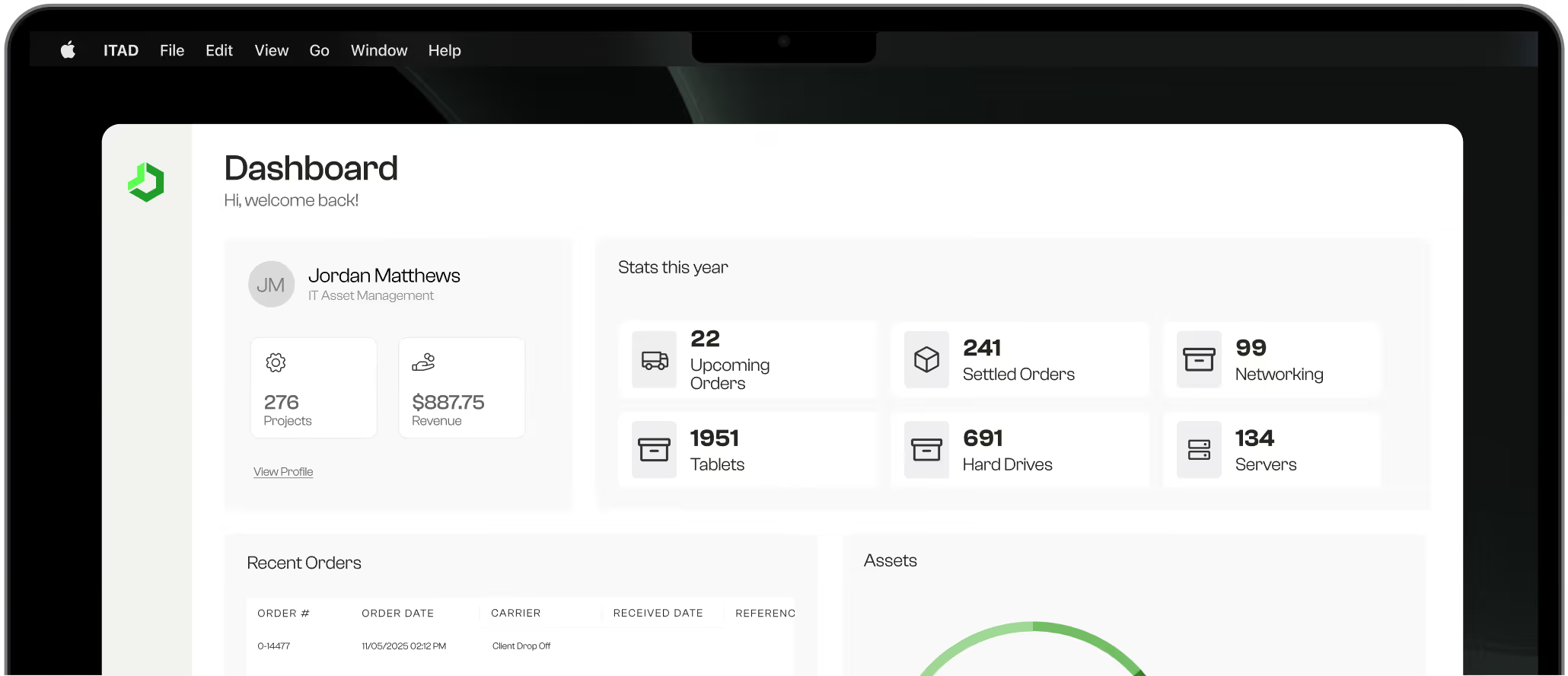
Operational Visibility Your Compliance Team Will Trust
A centralized platform for tracking assets, validating data destruction, managing documentation, and accessing audit-ready records.
Secure, certified, and operationally rigorous IT asset disposition.
Engineered for organizations that require documentation, auditability, and absolute accuracy.
R2v3-Certified Operations
Our facilities and workflows meet the highest global standards for ITAD, data security, reuse, and environmental compliance.
Audited NIST 800-88 Data Sanitization
Validated erasure and destruction methods with serialized reporting for every device.
Real-Time Chain-of-Custody Governance
Full lifecycle visibility, including pickup timestamps, handling logs, and disposition outcomes.
Automated and Standardized Workflows
System-driven testing, grading, and documentation ensure uniformity across high-volume and multi-site programs.
Optimized Asset Recovery
Transparent resale performance reporting delivers predictable ROI and audit-ready reconciliation.
A Certified, Fully Documented Process for Every Device
A centralized platform for tracking assets, validating data destruction, managing documentation, and accessing audit-ready records.
Secure Pickup
Serialized Intake
NIST-Compliant Data Destruction
Diagnostic Testing & Grading
Disposition Pathway
Certificates & Reporting
Sealed, tracked, and logged with geolocation and timestamp verification.
Every asset registered and assigned to your organization’s workflow.
Cryptographic erasure or physical destruction with serialized logs.
Automated diagnostic workflows ensure consistency and repeatability.
Remarketing or certified recycling aligned to governance standards.
COAs, CODs, and environmental reporting accessible on demand.
Operational Scale Backed by Measurable Accuracy
Aligned to the security, operational, and regulatory demands of modern IT organizations.
lbs of IT hardware processed annually
Fully certified and environmentally accountable.
Data Sanitization Accuracy
Validated through automation and multi-stage quality control.
Devices processed monthly
Capacity for distributed enterprise programs.
Proven results, verified by our clients
Technical Guidance for IT, Security, and Compliance Leaders
Stay ahead of evolving standards and best practices in secure IT asset disposition
Build a secure, certified ITAD program for your organization
Our team designs disposition strategies aligned to enterprise IT, security, and governance requirements.