Onsite Data Sanitization & Destruction
The security of your data is ITAD Techs’ top priority and sometimes that means coming to you for sensitive data sanitization or destruction needs.
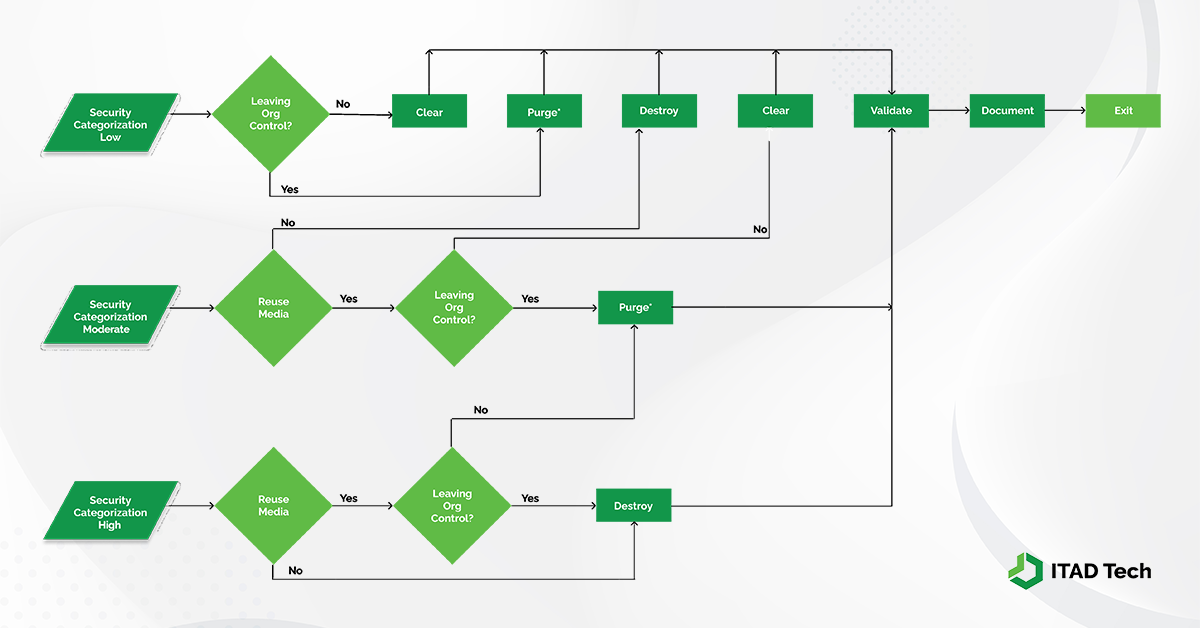
It is important to make informed decisions when it comes to data sanitization. The decision tree below is directly from NIST and it is key to deciding what form of data destruction is right for your company. Our onsite services cover our customers that prefer or need data sanitized or destroyed onsite. ITAD Tech specializes in the secure and complete erasure of data from hard drives, in strict accordance with the NIST 800-88 Rev 1 standard. Our expert team understands the importance of data privacy and security, offering you a reliable solution to ensure your sensitive information is thoroughly removed from retired or repurposed hard drives.
ITAD Tech highly recommends companies familiarize themselves with the NIST Special Publication 800-88 Revision 1, titled “Guidelines for Media Sanitization,” which provides comprehensive guidance on how to effectively sanitize or dispose of digital media to prevent unauthorized access to sensitive information. Media sanitization involves securely removing all data from storage devices before they are discarded, reused, or repurposed. The NIST publication defines three forms of media sanitization: Clear, Purge, and Destroy.
- Clear: Clearing refers to the process of overwriting storage media with non-sensitive data in order to remove all traces of the original data. This method ensures that the data is no longer accessible using normal software tools and techniques. The clear process should be performed using techniques that are appropriate for the media type and technology. Typically, this involves writing predefined patterns of data to the storage device, effectively obliterating the original content. The number of overwrite passes required can vary depending on the sensitivity of the data, the technology used, and the security requirements.
- Purge: Purging is a more thorough form of media sanitization. It involves rendering the data on the storage media irretrievable using methods designed to defeat both software and hardware-based data recovery techniques. Purging techniques are generally more effective for modern storage technologies such as solid-state drives (SSDs) that use wear-leveling algorithms and have built-in mechanisms that make data recovery after overwriting more challenging. Purging methods might include cryptographic erasure or ATA Secure Erase commands, both of which aim to make data recovery infeasible.
- Destroy: Destruction is the most extreme form of media sanitization. It involves rendering the storage media physically unusable and incapable of data recovery. ITAD Tech preferred physical destruction method is shredding. The goal is to physically break down the storage media into small fragments or particles so that any data they contained is unrecoverable. This method is often employed for media that have reached the end of their operational life or are deemed highly sensitive.
When selecting a media sanitization method, organizations should consider factors such as the sensitivity of the data, the technology used in the storage media, regulatory requirements, and the potential risks associated with the data falling into unauthorized hands. The NIST 800-88 publication provides a risk-based approach that helps organizations determine the appropriate level of sanitization for their specific needs.
It’s important to note that these forms of media sanitization are not mutually exclusive, and organizations may use a combination of methods depending on their requirements and resources. The choice of method should be part of an overall data disposal strategy that takes into account security, regulatory compliance, and cost-effectiveness. Additionally, organizations should regularly review and update their media sanitization practices to stay aligned with evolving technologies and security best practices.
Our NIST 800-88 Compliant Process:
- Consultation: Our process begins with a thorough consultation to understand your specific data sanitization requirements. Whether you’re a business or an individual, our experts will tailor our services to meet your needs.
- Data Assessment: Our certified professionals assess the data storage devices to be sanitized. This step helps determine the most suitable sanitization method for each drive, considering factors like drive type, capacity, and intended use.
- Sanitization Method Selection: Based on the assessment, we select the appropriate data sanitization method as outlined by the NIST 800-88 standard. Methods include Clear, Purge, and Destroy, each designed for different levels of data sensitivity and risk tolerance.
- Sanitization Execution: With the method chosen, we perform the sanitization process meticulously. Our technicians use advanced tools and software to ensure the complete removal of data from the hard drives, leaving no traces of sensitive information.
- Verification and Reporting: After sanitization, we conduct rigorous verification processes to confirm the successful eradication of data. A detailed report is generated for your records, outlining the devices sanitized, methods used, and results obtained.
- Certificate of Sanitization: Upon successful completion, we provide you with a Certificate of Sanitization that attests to the proper data removal in compliance with the NIST 800-88 standard. This certificate can be an essential document for audits and regulatory compliance.
Why Choose Our Services:
- NIST 800-88 Compliance: We adhere to the NIST 800-88 standard to ensure the highest level of data security and privacy in the sanitization process.
- Certified Experts: Our team comprises certified data security professionals with extensive experience in data sanitization and hard drive management.
- Customized Solutions: We understand that each client’s needs are unique. Our tailored approach ensures that your specific requirements are met efficiently and effectively.
- Verified Results: Our thorough verification processes guarantee the successful removal of data from hard drives, reducing the risk of data breaches and leaks.
- Audit Trail: The detailed report and Certificate of Sanitization serve as your audit trail, demonstrating compliance with data sanitization standards.
Get in Touch:
Protect your sensitive data and maintain regulatory compliance by choosing our NIST 800-88 compliant data sanitization services. Contact us today for a consultation and experience peace of mind knowing your data is in expert hands.